HTTP/2 Rapid Reset (CVE-2023-44487): Protocol Semantics Weaponized
In late 2023, one of the largest distributed denial-of-service (DDoS) campaigns in Internet history leveraged a protocol-level weakness in HTTP/2. The vulnerability — CVE-2023-44487, commonly known as HTTP/2 Rapid Reset — did not rely on amplification or bandwidth saturation.
It exploited protocol logic.
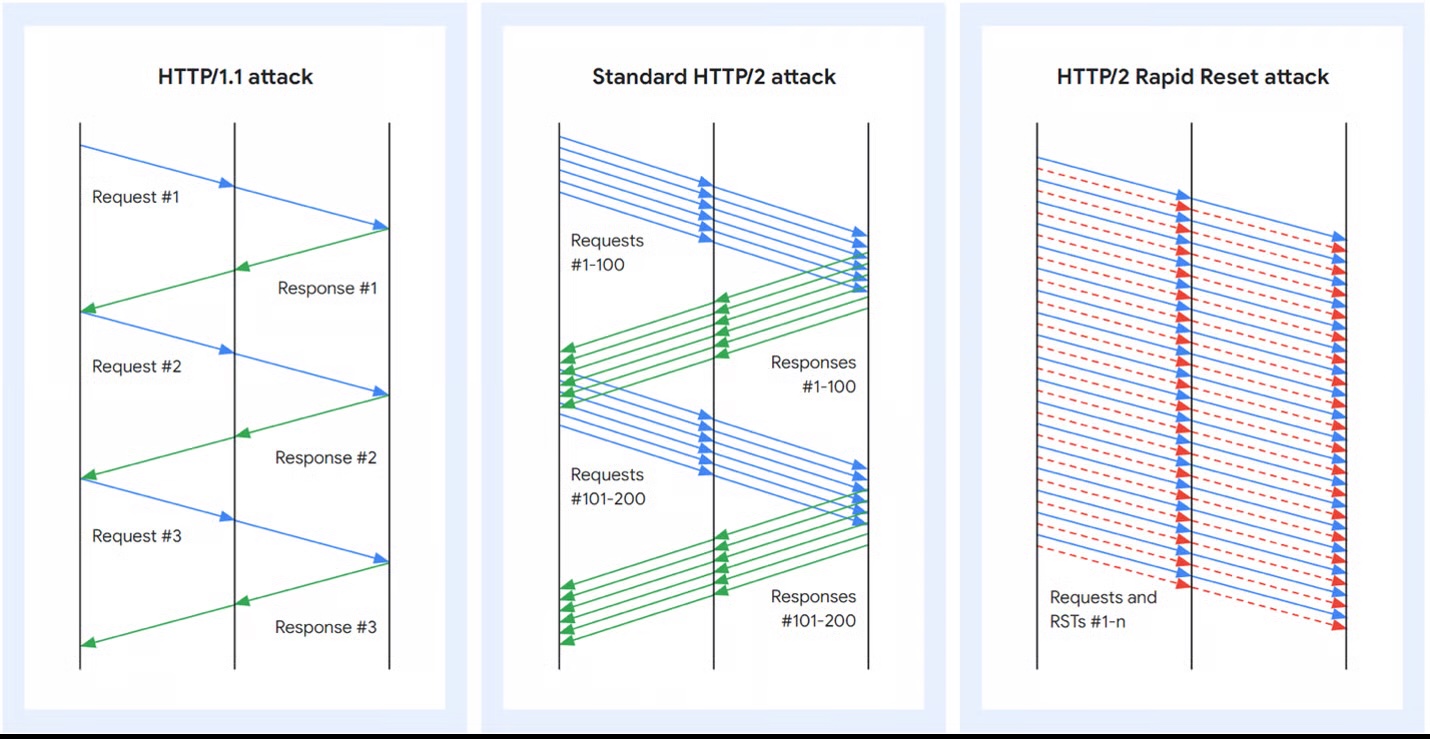
Protocol Context: HTTP/1.1 vs HTTP/2 Multiplexing#
HTTP/2 introduced multiplexing, allowing multiple concurrent request streams over a single TCP connection.
In HTTP/1.1:
- One request effectively blocks the next
- Head-of-line blocking
- Heavy reliance on multiple connections
In HTTP/2:
- Multiple independent streams per connection
- Framed messages
- Improved performance and reduced latency
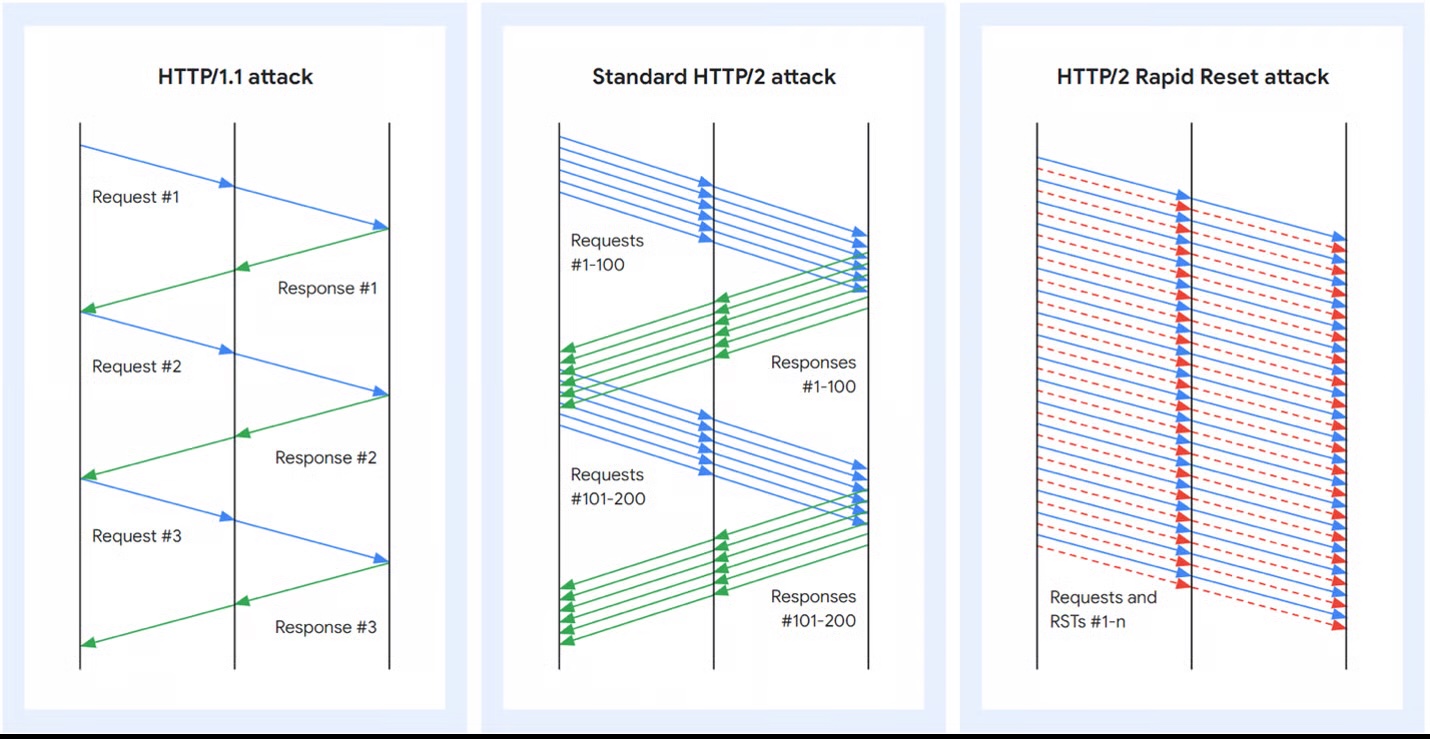
Figure 1. HTTP/1.1 and HTTP/2 request and response pattern (Courtesy of Google)
Multiplexing improved performance dramatically — but it changed server-side resource accounting.
Exploit Mechanism: RST_STREAM Abuse#
HTTP/2 allows a client to cancel a request stream using the RST_STREAM frame.
Normal stream lifecycle (simplified)#
- Client sends
HEADERS - Stream transitions
idle → open - Client sends
END_STREAM - Server processes request
- Server returns response and stream completes
Rapid Reset behavior#
- Client sends
HEADERS - Client immediately sends
RST_STREAM - Server begins processing work
- Stream closes before response delivery
- Client immediately opens another stream
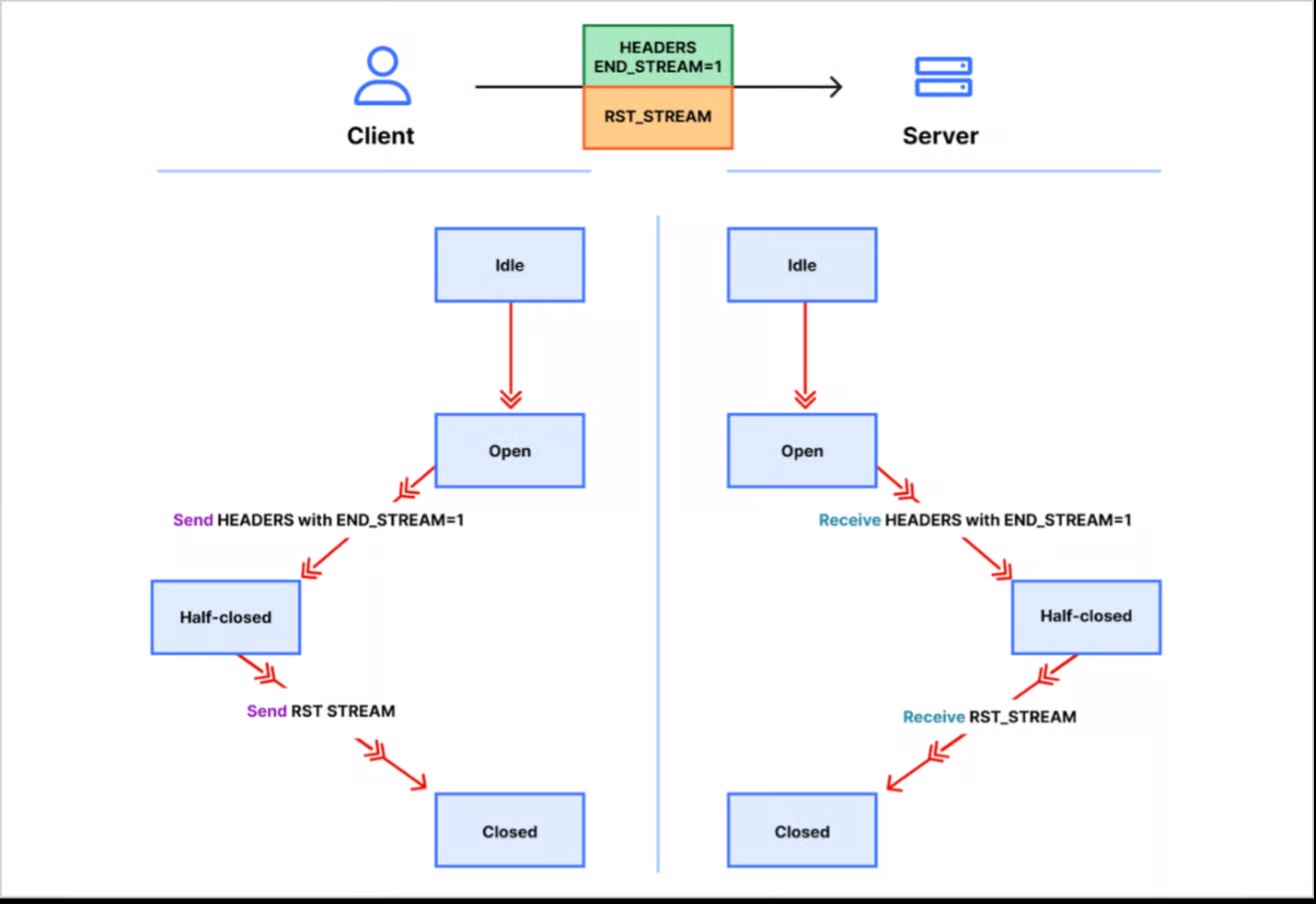
Figure 2. HTTP/2 stream state transitions (Courtesy of Cloudflare)
The critical insight:
When a client cancels a stream, it instantly regains the ability to open another stream.
Because concurrency limits apply to active streams, rapidly closed streams allow attackers to avoid hitting thresholds while still forcing server work.
Operational Impact: Why This Scales#
This vulnerability was actively exploited between August and October 2023.
Targets included:
- AWS
- Cloudflare
Reported peaks exceeded hundreds of millions of requests per second.
Unlike volumetric DDoS attacks, Rapid Reset:
- Does not rely on bandwidth saturation
- Exploits application-layer work and request parsing
- Scales efficiently per TCP connection
- Focuses on CPU and request handling exhaustion
Detection: What “Bad” Looks Like in Telemetry#
A public testing tool was released to identify vulnerable implementations. At a high level, detection attempts to measure whether a server:
- allows rapid create/reset cycles without penalty,
- continues processing work despite immediate resets, and
- fails to terminate abusive connections.
1. Objective
Determine whether the service enforces effective controls against rapid create/reset stream behavior that can be weaponized for application-layer resource exhaustion.
2. Evidence
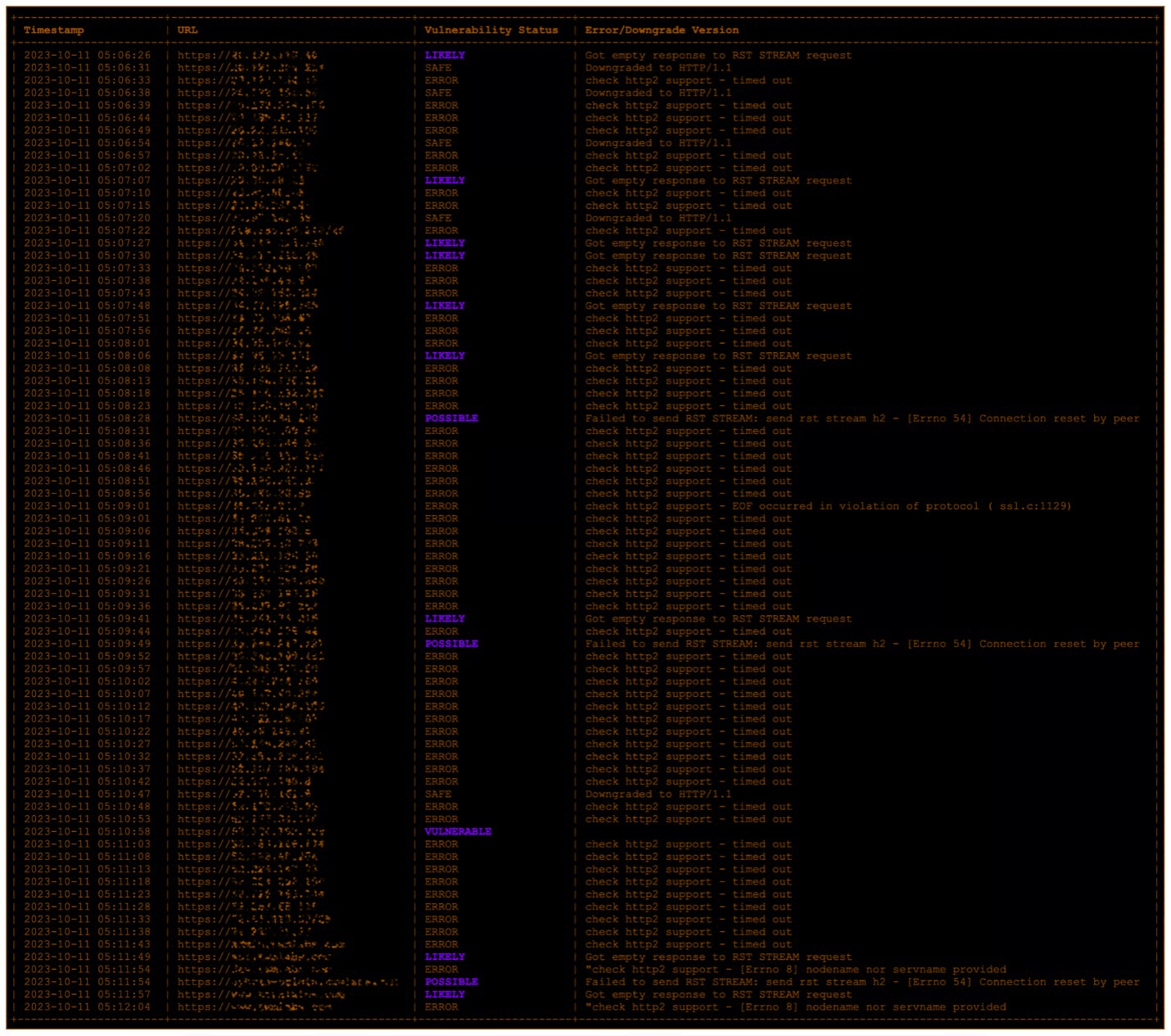
Evidence Type: Tool Output (HTTP/2 rapid reset test)
Condition: Stream opened and immediately reset (RST_STREAM)
Expected Control Behavior:
- Rate limit resets OR
- Penalize excessive resets OR
- Terminate abusive connections
Indicator of Exposure:
- Sustained rapid create/reset cycles without throttling or termination3. Interpretation
If the service allows continuous rapid creation and cancellation of streams without throttling, penalty, or connection termination, it is likely vulnerable (or functionally exposed) to Rapid Reset-style abuse.
Mitigation: Protocol-Aware Controls#
Effective defense requires stream-lifecycle-aware controls, not just request-rate limits.
1) Reset-aware rate limiting#
Monitor abnormal reset-to-completion ratios and penalize excessive resets.
2) Stream lifetime controls#
Enforce maximum streams per connection and terminate abusive connections.
3) Edge-level L7 protection#
Use reverse proxies, adaptive filtering, and intelligent request shaping that understands HTTP/2 behavior.
Major vendors patched implementations to properly account for rapid resets and enforce connection termination under abuse conditions.
Strategic Takeaways#
CVE-2023-44487 demonstrates:
- Protocol semantics can be weaponized
- Performance optimizations expand attack surface
- Concurrency limits alone are insufficient
- Application-layer DDoS is increasingly logic-driven
Modern defense should monitor:
- Stream lifecycle behavior
- Cancellation frequency
- CPU-bound exhaustion patterns
- Application-layer economics
HTTP/2 Rapid Reset is a reminder that performance and security evolve together.
References#
Cloudflare – HTTP/2 Rapid Reset Analysis
https://blog.cloudflare.com/technical-breakdown-http2-rapid-reset-ddos-attack/
Google – The Novel HTTP/2 Rapid Reset DDoS Attack
https://cloud.google.com/blog/products/identity-security/how-it-works-the-novel-http2-rapid-reset-ddos-attack
AWS Advisory – CVE-2023-44487
https://aws.amazon.com/security/security-bulletins/AWS-2023-011/
NGINX Impact Notice
https://www.nginx.com/blog/http-2-rapid-reset-attack-impacting-nginx-products/
Microsoft Response
https://msrc.microsoft.com/blog/2023/10/microsoft-response-to-distributed-denial-of-service-ddos-attacks-against-http-2/
CVE Record
https://www.cve.org/CVERecord?id=CVE-2023-44487
Detection Tool
https://github.com/bcdannyboy/CVE-2023-44487/